Yes, I’ll look into how hardened that unsafe browser is, because that would be an ideal solution for me. Thank you very much.
- 13 Posts
- 100 Comments
Is that browser hardened to the extent the tor browser is? I looked this up and have seen conflicting reports. If it is, that would probably be a viable solution.
I appreciate your attempt to help, but I do also realize that what I’m asking for is rather niche and may not exist.
Do you need it to be amnesiac? The very thing that defines Tails*.
Yes. A persistent storage feature would be nice but isn’t a requirement.
What’s wrong with Tor? Is your threat model so paranoid that you (somehow) don’t even trust Tor? Or, are you not in favor of its (relatively) low bandwidth? Or, is privacy and/or security not even a thing you seek after to begin with? Or, at least not beyond what your average distro provides already*.
The reason I don’t want to use Tor is because I will only connect to plain web websites where I don’t care if they know my IP. I also find that CloudFlare and other services can block Tor which sometimes causes issues with my work.
What do you intend to do with it? Daily drive it? If so, do you need persistence?
I mainly plan on isolating certain browser-based work I’m doing with other work on my computer. As I said before, persistence would be nice but is not necessary.
What does “Tails without Tor reliance” provide/offer you beyond a LiveUSB from any other distro? Or, rather, what do you hope it will provide/offer you?
I hope it would offer me a highly hardened environment to do work in, without the requirement to set it up every time on other liveusb OSes.
To put this all together, I want an amnesiac live USB hardened(browser, kernel) environment that does not use Tor.
That needs tor, like I said in the post I don’t want tor reliance.
Closest I found there is Secure-K which I might check out.
I use firefox and am actively looking to change to something, potentially librewolf.
Edit: just installed librewolf. it’s super clean and I’m glad I got it. replaced firefox almost instantly.
This list seems to leave out a good amount of distros but overall not too bad.
Magisk is the only one I know of.

 96·2 months ago
96·2 months agoSo glad people are dipping out of plex.

 0·2 months ago
0·2 months agoSorry! The ip was wrong, the nginx vm is 192.168.101.85. edited

 2·2 months ago
2·2 months agoI think NGINX has the best reverse proxy

 0·2 months ago
0·2 months agoI ended up just installing Alma Linux again. Thank you very much for your help.

 7·2 months ago
7·2 months agoDO NOT follow my lead, my backup solution is scuffed at best.
3:
I have:
- RAID1 array w/ 2 drives
- Photos on the device that took them
- Photos on a random old hard drive pulled from an ancient apple mac.
2:
I’ve got a hard drive and flash memory?
1:
Don’t have this at all, the closest is that my phone is off-site half of the day.

 0·2 months ago
0·2 months ago192.168.101.4is the alma guest. It’s got port 22 open and I can ssh into it from the host computer.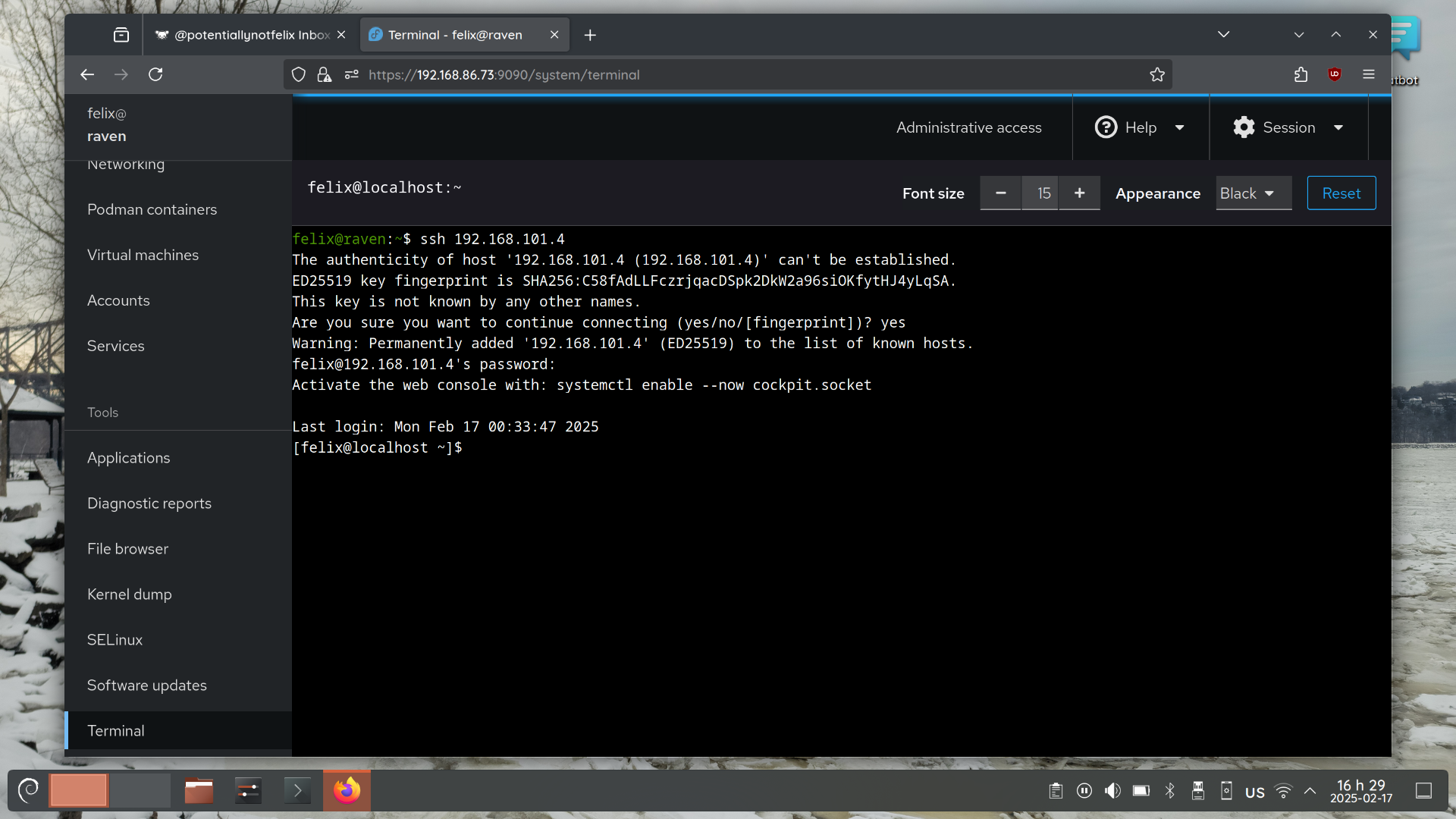
iptables -nvL on Alma returns:
Chain INPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain FORWARD (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destinationI believe this means it automatically accepts connections.
IMO this makes it unlikely that the guest is the issue.

 0·2 months ago
0·2 months agossh -v returns:
OpenSSH_9.2p1 Debian-2+deb12u4, OpenSSL 3.0.15 3 Sep 2024 debug1: Reading configuration data /etc/ssh/ssh_config debug1: /etc/ssh/ssh_config line 19: include /etc/ssh/ssh_config.d/*.conf matched no files debug1: /etc/ssh/ssh_config line 21: Applying options for * debug1: Connecting to 192.168.86.73 [192.168.86.73] port 2222. debug1: connect to address 192.168.86.73 port 2222: Connection refused ssh: connect to host 192.168.86.73 port 2222: Connection refused

 0·2 months ago
0·2 months agoNo firewalls on the client, but iptables on host and guest. guest has no rules just allow all, and host rules are listed in the post.

 0·2 months ago
0·2 months agosysctl net.ipv4.ip_forwardreturns:net.ipv4.ip_forward = 1So I’m pretty sure that this is already enabled. Thanks for your answer!

 0·2 months ago
0·2 months agoFrom the
iptablesmanpage:--to offset Set the offset from which it starts looking for any matching. If not passed, default is the packet size. ... --to-destination ipaddr-ipaddr Address range to round-robin over.This seems to do something, but the port still appears as closed.
iptables -nvLreturns:Chain INPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain FORWARD (policy ACCEPT 369 packets, 54387 bytes) pkts bytes target prot opt in out source destination 5 300 ACCEPT 6 -- * virbr1 0.0.0.0/0 192.168.101.4 tcp dpt:22 84 6689 ACCEPT 0 -- * br-392a16e9359d 0.0.0.0/0 0.0.0.0/0 ctstate RELATED,ESTABLISHED 7 418 DOCKER 0 -- * br-392a16e9359d 0.0.0.0/0 0.0.0.0/0 146 9410 ACCEPT 0 -- br-392a16e9359d !br-392a16e9359d 0.0.0.0/0 0.0.0.0/0 0 0 ACCEPT 0 -- br-392a16e9359d br-392a16e9359d 0.0.0.0/0 0.0.0.0/0 Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destinationI’ve omitted some listings that were labelled as docker.
iptables -t nat -nvLreturns:Chain PREROUTING (policy ACCEPT 626 packets, 90758 bytes) pkts bytes target prot opt in out source destination 5 300 DNAT 6 -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:2222 to:192.168.101.4:22 Chain INPUT (policy ACCEPT 0 packets, 0 bytes) pkts bytes target prot opt in out source destination Chain OUTPUT (policy ACCEPT 154 packets, 12278 bytes) pkts bytes target prot opt in out source destination 0 0 DOCKER 0 -- * * 0.0.0.0/0 !127.0.0.0/8 ADDRTYPE match dst-type LOCAL Chain POSTROUTING (policy ACCEPT 290 packets, 22404 bytes) pkts bytes target prot opt in out source destination 0 0 MASQUERADE 0 -- * !br-392a16e9359d 172.18.0.0/16 0.0.0.0/0I’ve also omitted some listings that were labelled as docker.
After running the
sshcommand, the bytes seem to increase. After 1 ssh attempt:7 420 DNAT 6 -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:2222 to:192.168.101.4:22After another ssh attempt:
8 480 DNAT 6 -- * * 0.0.0.0/0 0.0.0.0/0 tcp dpt:2222 to:192.168.101.4:22



I don’t know about yts, but last time I checked 1337x is totally safe as long as you download from trustworthy sources.