Weaponized Autism. Less than a second in lag. I love our community.
Actually the dude was looking to profile some other program of his own and tried to reduce nose on the machine. That’s when he noticed sshds creating a load of load with no reason.
What a load.
I just updated xz in my system. Thanks Lemmy!
On any server, you want unattended upgrades.
Depends, for example Debian unattended-upgrade caused system restarts after many updates that was extremely inconvenient for me because I have a more manual bringup process. I had restarts turned off in its settings and it still restarted.
I uninstalled it and have not one single unwanted restart since then, so manual upgrades it is.
I’ve been using it for 10+ years on servers and it’s not been an issue for me.
What did i miss?
OpenSSH backdoor
Openssh backdoor via a trojan’ed release of liblzma
opensourceautists win!Opensautists
To be fair, we only know of this one. There may well be other open source backdoors floating around with no detection. Was heartbleed really an accident?
Yeah he didn’t find the right unmaintained project. There are many many many cs undergrads starting projects that will become unmaintained pretty soon.
True. And the “given enough eyeballs, all bugs are shallow” is a neat sounding thing from the past when the amount of code lines was not as much as now. Sometimes it is scary to see how long a vulnerability in the Linux kernel had been there for years, “waiting” to be exploited.
Still far better than a proprietary kernel made by a tech corp, carried hardly changed from release to release, even fewer people maintain, and if they do they might well be adding a backdoor themselves for their government agency friends.
Exactly.
true, opensource can be flawed, but it’s certain less flawed than a closed source alternatives
Eh, autism jokes are not funny. Ableism isn’t funny.
The only real downside on the open source side is that the fix is also public, and thus the recipe how to exploit the backdoor.
If there’s a massive CVE on a closed source system, you get a super high-level description of the issue and that’s it.
If there’s one on an open source system, you get ready-made “proof of concepts” on github that any script kiddy can exploit.
And since not every software can be updated instantly, you are left with millions of vulnerable servers/PCs and a lot of happy script kiddies.
See, for example, Log4Shell.
Even in open source, responsible disclosure is generally possible.
See, e.g. Spectre/Meltdown, where they worked privately with high level Linux Kernel developers for months to have patches ready on all supported branches before they made the vulnerability public
Was the transition into management easy for you, or was it a slow acceptance?
Oh, we play dumb ad-hominem without any basis in reality?
I can play this too: Was your last school homework hard?
bUt gUyS WhAt aBoUt sEcUrItY ThRoUgH ObScUrItY??
hEy, yOu lEaRnEd A bUzZwOrD aNd rEcEnTlY dIsCoVeReD tHe sHiFt KeY!!! cOnGrAtS!?!
hEy, yOu lEaRnEd A bUzZwOrD aNd rEcEnTlY dIsCoVeReD tHe sHiFt KeY!!! cOnGrAtS!?!
hEy, yOu lEaRnEd A bUzZwOrD aNd rEcEnTlY dIsCoVeReD tHe sHiFt KeY!!! cOnGrAtS!?!
Honestly, for closed source software the POCs are also immediately available. Lots of threat actors just use patch diffing.
These days vulnerabilities are at times also patched with other non-related commits to conceal what exactly has changed.
In this case it seems the backdoor is only usable with someone who has the correct key. Seeing and reverting something fishy is in some cases, like this easier than finding an exploit. It takes a lot of time in this case to figure out what goes on.
Fixing a bug never automatically give an easy to use exploit for script kiddies
If your security relies on hidden information then it’s at risk of being broken at any time by someone who will find the information in some way. Open source security is so much stronger because it works independently of system knowledge. See all the open source cryptography that secures the web for example.
Open source poc and fix increases awareness of issues and helps everyone to make progress. You will also get much more eyes to verify your analysis and fix, as well as people checking if there could other consequences in other systems. Some security specialists are probably going to create techniques to detect this kind of sophisticated attack in the future.
This doesn’t happen with closed source.
If some system company/administrator is too lazy to update, the fault is on them, not on the person who made all the information available for your to understand and fix the issue.Crowd sourcing vulnerability analysis and detection doesn’t make open source software inherently more secure.
Closed source software has its place and it isn’t inherently evil or bad.
This event shows the good and bad of the open source software world but says NOTHING about closed source software.
Crowd sourcing vulnerability analysis and detection doesn’t make open source software inherently more secure.
It does, because many more eyes can find issues, as illustrated by this story.
Closed source isn’t inherently bad, but it’s worse than open source in many cases including security.
I think you’re the only one here thinking publishing PoC is bad.
This is literally how I make my living and this is the only comment I’ve made so I’m not sure where you get the idea I think publishing vulnerabilities and PoC are bad … again I literally do this for a living.
Finding vulnerabilities and reporting them is literally what pays my mortgage. Open Source, Closed Source, they both have their merits but to say one is inherently more secure because of the reasons you’re specifying is tacitly false.
My comment is literally only about what you said which pushes a thought that slides to far in one direction. There is a reason no nation state will open source their military hardware.
Then please explain why the reasons specified here are false belong that argument from authority.
I don’t need to repeat myself but that’s all I’d be doing.
You’re making the argument that open source software inherently does this better and I’m telling you that you’re wrong. I’m going to cite myself, a 20 year veteran in the field.
It can do it better and often times it does work out this way.
Closed source software also has value and use and for its own set of reasons could make the argument that it is more secure because of access controls and supply chain management and traditional security mechanisms.
I think you read what I wrote as a “no you’re entirely wrong” whereas what I said was “you’re asserting things that aren’t true which is weakening the argument”
Frankly though given the lack of response to what I actually said by anyone I’m just going to rest on knowing in the real world my input is considered valid, here where we’re being fanatics … idk for all you know I’m a bot spewing AI generated drivel.
Maybe the disconnect here is I’m talking about practical application because of experience vs theoretical application because of ideology.
No I don’t think you said I was entirely wrong, that part was clear enough.
My issue is more with your argument from authority and personal experience. It is very easy to be biased by personal experience, especially when it brings good money.
access controls and supply chain management and traditional security mechanisms.
So I’ll put my personal experience too (which is also a low value argument). From the outside it may seem this is well done in big companies. But the reality is that this is often a big mess and security often depends on some guy, if any, actually having some standards and enforcing them, until they leave because the company doesn’t value those tasks. But since it’s closed source, nobody knows about it. With open source, there’s more chance more people will look at this system and find issues.
I don’t doubt some ultra sensitive systems like nuclear weapons have a functional closed source security process because the government understands the risk well enough. But I think there are way more closed source systems, at lower danger level but which still impacts people’s security, that are managed with a much lower standard than if they were open-sourced.
It does, because many more eyes can find issues, as illustrated by this story.
This story illustrates that some eyes can find some issues. For proper discussion we need proper data and ratios, only then we could compare. How many issues there are in open and closed source software? How many of them are getting fixed? Unfortunately, we don’t have this data.
But this issue wasn’t found because of code analysis per se, but because of microbenchmarking.
If the vulnerability is in the wild, what other security mechanisms do you have until it’s patched?
In this case, downgrading to the not affected version. If there’s no possible downgrade, stopping the compromised system until it is fixed.
Keeping the vulnerable system up because you think nobody else should know is a bet, I don’t think it’s sound. State actors are investing a lot to find and exploit those vulnerabilities, in this case probably even funded the implementation of the vulnerability, so I think you should assume that any vulnerability you discover is already used.
I’m pretty sire there are plenty of ways to exploit proprietary systems. You can’t stop the power of the keyboard
this is why we invented responsible disclosure, which is a thing companies like apple do even. Although in this case, this was the very beginning of what seemed to be a rollout, so if it does effect systems, it’s not very many. And if they are affected. The solution is pretty obvious.
Don’t be a dunce, report responsibly.
I love free software community. This is one of the things free software was created. The community defends its users.
I second this. I love to feel part of a community even tho I could have never found the backdoor, let alone fix it.
everytime this happens i become unexplainably happy.
There’s just something about a community doing it’s fucking job that gets me so normal feeling.
I’ve gotten back into tinkering on a little Rust game project, it has about a dozen dependencies on various math and gamedev libraries. When I go to build (just like with npm in my JavaScript projects) cargo needs to download and build just over 200 projects. 3 of them build and run “install scripts” which are just also rust programs. I know this because my anti-virus flagged each of them and I had to allow them through so my little roguelike would build.
Like, what are we even suppose to tell “normal people” about security? “Yeah, don’t download files from people you don’t trust and never run executables from the web. How do I install this programming utility? Blindly run code from over 300 people and hope none of them wanted to sneak something malicious in there.”
I don’t want to go back to the days of hand chisling every routine into bare silicon by hand, but i feel l like there must be a better system we just haven’t devised yet.
It’s a really wicked problem to be sure. There is work underway in a bunch of places around different approaches to this; take a look at SBoM (software bill-of-materials) and reproducible builds. Doesn’t totally address the trust issue (the malicious xz releases had good gpg signatures from a trusted contributor), but makes it easier to spot binary tampering.
+1
Shameless plug to the OSS Review Toolkit project (https://oss-review-toolkit.org/ort/) which analyze your package manager, build a dependency tree and generates a SBOM for you. It can also check for vulnerabilitiea with the help of VulnerableCode.
It is mainly aimed at OSS Compliance though.
(I am a contributor)
I’m not familiar with rust but at least for java there’s a owasp plugin that tells you if you’re using an unsafe library.
Like, what are we even suppose
supposed
to tell “normal people” about security? “Yeah, don’t download files from people you don’t trust and never run executables from the web. How do I install this programming utility? Blindly run code from over 300 people and hope none of them wanted to sneak something malicious in there.”
You’re starting to come to an interesting realization about the state of ‘modern’ programming and the risks we saw coming 20 years ago.
I don’t want to go back to the days […]
You don’t need to trade convenience for safety, but having worked in OS Security I would recommend it.
Pulling in random stuff you haven’t validated should feel really uncomfortable as a professional.
Do you really need to download new versions at every build? I thought it was common practice to use the oldest safe version of a dependency that offers the functionality you want. That way your project can run on less up to date systems.
Most softwares do not include detailed security fixes in the change log for people to check; and many of these security fixes are in dependencies, so it is unlikely to be documented by the software available to the end user.
So most of the time, the safest “oldest safe” version is just the latest version.
So only protects like Debian do security backports?
Backports for supported versions sure,.
That’s why there is an incentive to limit support to latest and maybe one previous release, it saves on the backporting burden.
Okay, but are you still going to audit 200 individual dependencies even once?
That’s what the “oldest safe version” is supposed to address.
Because everything is labeled safe and unsafe, right?
Your snark is tremendously conducive for a conversation. Go touch some grass.
Which is why you shouldn’t do that. Dependency nightmare is a real problem many developers face. More to the point they impose it on you as well if you are by any reason forced to use their software. Well established libraries are gateway to this. People are getting out of their way to complicate lives to themselves and massive amount of others just so they could avoid writing a function or two. Biggest absurdity I like to point out to people is the existence of
is-numberNPM package, which does that. It has 2300 dependent projects on it!!! Manifest file for said package is bigger than the source. And the author had the hubris to “release it under MIT”. How can you claim copyright onnum - num === 0?On all the projects I manage I don’t allow new dependencies unless they are absolutely needed and can’t be easily re-implemented. And even then they’d have to be already in the Debian respository since it’s a good and easy way to ensure quick fixes and patching should it be needed. Sometimes alternative to what we wanted to use already is in repo, then we implement using different approach. We only have few Python modules that are not available in repo.
Managing project complexity is a hard thing and dependencies especially have a nasty habit of creeping up. I might be too rigid or old-school or whatever you want to call it, but hey at least we didn’t get our SSH keys stolen by NPM package.
THIS.
I do not get why people don’t learn from Node/NPM: If your language has no exhaustive standard library the community ends up reinventing the wheel and each real world program has hundreds of dependencies (or thousands).
Instead of throwing new features at Rust the maintainers should focus on growing a trusted standard library and improve tooling, but that is less fun I assume.
Can you give some examples of things missing from Rust standard library?
Easily, just look at the standard libraries of Java/Python and Golang! :-P
To get one thing out of the way: Each standard library has dark corners with bad APIs and outdated modules. IMHO it is a tradeoff, and from my experience even a bad standard library works better than everyone reinvents their small module. If you want to compare it to human languages: Having no standard library is like agreeing on the English grammar, but everyone mostly makes up their own words, which makes communication challenging.
My examples of missing items from the Rust standard library (correct me, if I am wrong, not a Rust user for many reasons):
- Cross platform GUI library (see SWING/Tk)
- Enough bits to create a server
- Full set of data structures and algorithms
- Full set of serialization format processing XML/JSON/YAML/CVS/INI files
- HTTP(S) server for production with support for letsencrypt etc.
Things I don’t know about if they are provided by a Rust standard library:
- Go like communication channels
- High level parallelism constructs (like Tokyo etc.)
My point is, to provide good enough defaults in a standard library which everybody knows/are well documented and taught. If someone has special needs, they always can come up with a library. Further, if something in the standard library gets obsolete, it can easily be deprecated.
Python doesn’t have a production web server in its standard library. Neither does Java. Those are external programs or libraries. C# is the only language I know that comes with an official production grade server, and that’s still a separate package (IIS).
Rust has a set of recommended data structures in their standard libraries too: https://doc.rust-lang.org/std/collections/index.html
I don’t know what algorithms you are looking for so can’t answer here.
The rest I don’t think are included in Rust. Then again they aren’t included in most languages standard libraries.
Golangs web server is production grade and used in production. (Of course everyone uses some high performance proxy like NGINX for serving static pages, that’s another story.)
Technically you are right that java has no production web server, which I don’t like, OTOH Java has standard APIs WebServers and Spring is the defacto standard for web applications. (I totally would not mind to move Spring into the OpenJDK.)
My point is simple: Instead of having Rust edtion 2020, 2021 etc. and tweaking the syntax ad infinitum, I’d rather have a community which invests in a good/broad standard library and good tooling.
The only platform widely used in production w/o a big standard library is Node.js/JavaScript, mostly for historical reasons and look at the problems that Node.js has for a decade now because of the missing standard library.
I thought they already had decent tooling and standard libraries?
It does, but the person you reply to apparently expects a standard library to contain an ECS and a rendering engine.
Debian actually started to collect and maintain packages of the most important rust crates. You can use that as a source for cargo
Researchers have found a malicious backdoor in a compression tool that made its way into widely used Linux distributions, including those from Red Hat and Debian.
those from Red Hat
Not the enterprise stuff; just the beta mayflies.
Yeah they messed up once. It’s still miles better than just not having someone looking at the included stuff
You’d think this would be common sense…
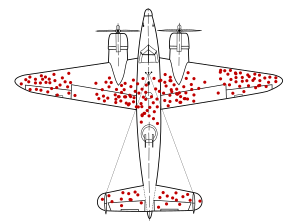
For the uninitiated, this is a representation of the Survivors Bias.
Essentially, the red dots represent bullet holes from aircraft which returned from battle.
If you were to ask someone which places should be reinforced with armour, someone who has the Survivors Bias would say “where the red dots are”, whereas people who know anything about engineering would say “everywhere else!”
To put it another way. If an aliens looked at survivors at war and saw very few had head wounds, they might be confused why we put so much emphasis on wearing a helmet, since we almost never get hurt there.
A true fact: Did you know wearing a helmet increases your chances of dying of cancer.
A true fact: Did you know wearing a helmet increases your chances of dying of cancer.
Rofl I love this. Great comment
What are you saying? That there are people doing the top version (“I want a backdoor / I ask the corpo to grant me access”) for FOSS but they’re less likely to get caught if they don’t do all the gymnastics?
OP is referring to a backdoor that was found. It apparently modified behaviour in a way that was noticeable to humans, suggesting that it was built by an unskilled adversary.
It’s a safe bet that there are others (in FOSS) that remain undiscovered. We know that skilled adversaries can produce pretty amazing attacks (e.g. stuxnet), so it seems likely that similar vulnerabilities remain in other FOSS packages.
It’s a safe bet that there are others (in FOSS) that remain undiscovered.
I agree, but I don’t think that image (about survivors’ bias) applies to the op meme then, as that would imply that it only seems like open source backdoors are convoluted because we’ve not found the simple/obvious ones
Getting noticed because of a 300ms delay at startup by a person that is not a security researcher or even a programmer after doing all that would be depressing honestly.
i feel like the mental gymnastics should end with a rake step
Queensbury Rules init.
Init as in 'contraction of "isnt it”’? Or as in ‘initialize’?
It’s about the complex rationalizations used to create excuses (pretexts).
The original is this:

Wow this is great
Alright I won’t argue about that specific version’s point, but this is basically a template for constructing a strawman argument.
I feel like that’s really crappy non-vegan mental gymnastics. I think veganism is morally superior, but I really want to show mine off, just because I’m offended by how stupid all these are-the fact I know they’re real makes me more ashamed of eating that yogurt earlier than any amount of chatt slavery or butchery ever will.
Lmao this is the first time I’m seeing this format, I like the content so far.
It is pretty funny, I bet he’s kicking himself right now for it.
related blog - https://robmensching.com/blog/posts/2024/03/30/a-microcosm-of-the-interactions-in-open-source-projects/
Make no mistake. This is the way it works.
It needs to change.
Agreed.